Under state laws like the California Consumer Privacy Act (CCPA), consumers finally have a right to control what happens with their data. Under CCPA, consumers can enlist an authorized agent to help them exercise these rights, granting the agent authority to submit data requests to companies on their behalf. Consumer Reports believes privacy is a right all consumers deserve, and our R&D team has done extensive work to research the existing data rights ecosystem and pilot sending data rights requests on behalf of consumers.
A few months ago, we launched our own authorized agent app, Permission Slip, in private beta. Through Permission Slip, we’ve sent data rights requests to companies on behalf of hundreds of consumers, giving us visibility into how different companies process authorized agent requests. Along the way, we found that the process differs significantly from company to company.
I joined Consumer Reports as a summer research fellow via Cornell’s Public Interest Tech PhD Fellowship with the goal of digging into the data generated from Permission Slip’s private beta between March 2022 to June 2022. I wanted to analyze how companies took in and responded to CCPA requests sent by Permission Slip, and see if I could deduce any patterns; such patterns might help the Permission Slip team more effectively deliver CCPA requests to companies, and can help other authorized agents adjust their practices to improve request success rates for the consumers they serve.
In this blog post, I’ll walk through my research methods and outline five flows our team encountered when submitting CCPA data rights requests to companies on consumers’ behalf.
Methods
The data that informed this analysis was generated from the first Permission Slip private beta program, which ran from March 2022 and June 2022. We had 157 consumers enroll in the Permission Slip beta, and offered to facilitate CCPA data rights requests for these users with 32 companies. All in all, we sent 1,666 requests for consumers during this time. Some were requests to opt-out of the sale of their data; others were requests to delete their data.
Because our analysis only considered 32 companies supported within the Permission Slip app, our sample is not representative of all companies that have CCPA processes. Notably, our sample is heavily biased towards companies that accept CCPA requests via email. We selected companies for the app based on what consumers would find relevant and useful, as opposed to companies that would make this research and analysis comprehensive. Moreover, our sample only includes processes for delete and opt-out requests, meaning consumer requests to access a copy of their data were not considered.
Even though this cohort is not representative of the market, analyzing some of the first data available on authorized agent CCPA flows can still provide valuable insights as we seek to improve the Permission Slip service. We hope these findings can also be of service to other authorized agents attempting to scale their operations.
In order to form categories that were relevant to authorized agents, we framed our analysis in terms of the following questions:
- What is required from the consumer, and what is required from the agent?
- Who is taking action at any point in the process?
- When are requests being responded to and completed?
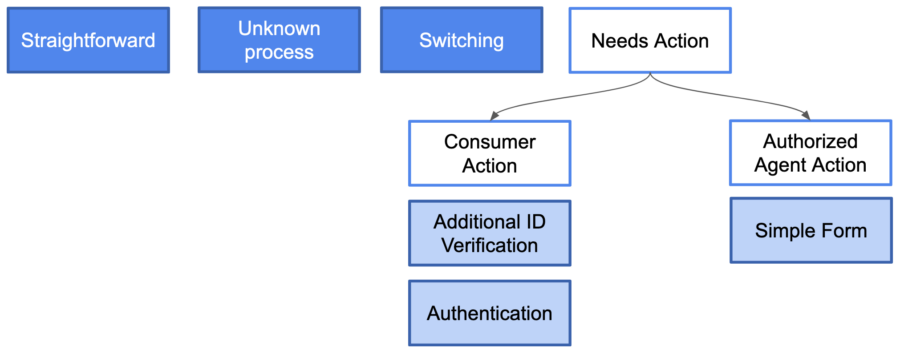
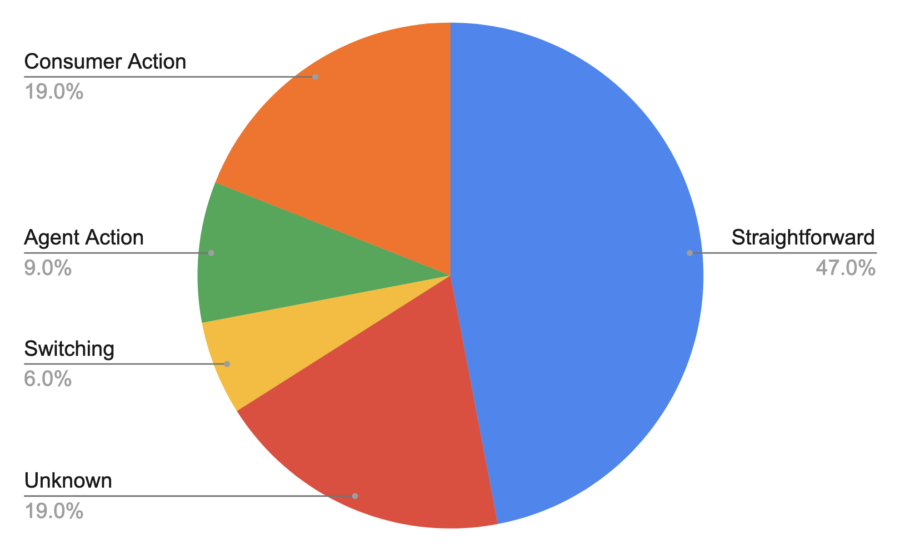
After compiling data on these questions for each of the 32 companies in the beta, we categorized the CCPA flows we encountered into five broad categories: straightforward, unknown, switching, authorized agent action, and consumer action flows.
(1) Straightforward Flows
The most common CCPA request flow we saw from companies was also one of the simplest to handle: the straightforward flow. 15 of the 32 companies in our sample had straightforward flows, which means the company processed a CCPA request sent on behalf of a consumer without any additional action needed from the agent or consumer. In rare cases, when the information provided by the authorized agent was insufficient to locate the specific consumer’s data, the company would notify the authorized agent directly that they were unable to find a match. These streamlined flows have a low strain on authorized agents’ resources and are an excellent fit for agents’ operations.
(2) Unknown Flows
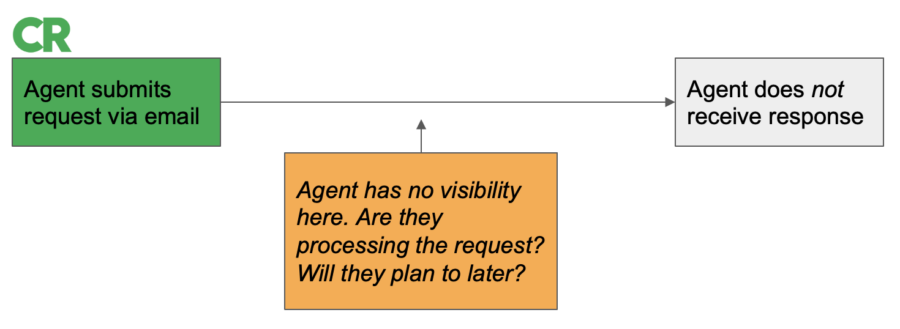
6 of the companies we analyzed did not respond to CCPA requests from authorized agents. Because in these cases Permission Slip had no visibility into what happened after the request was sent, we refer to these companies as having unknown flows. Unlike straightforward flows, unknown flows require routine effort: Periodic follow-up is necessary for agents to attempt to receive confirmation that requests have been received and completed.
Agents might consider sending follow-ups to these companies in batches on a regular cadence to incite more responsiveness. In some cases, companies that do not respond to requests may be in violation of the CCPA regulations. Because authorized agents can represent multiple consumers, they are in a unique position to remind companies of their CCPA compliance obligations, and possibly engage with companies to help determine more effective processes for completing requests.
(3) Switching Flows
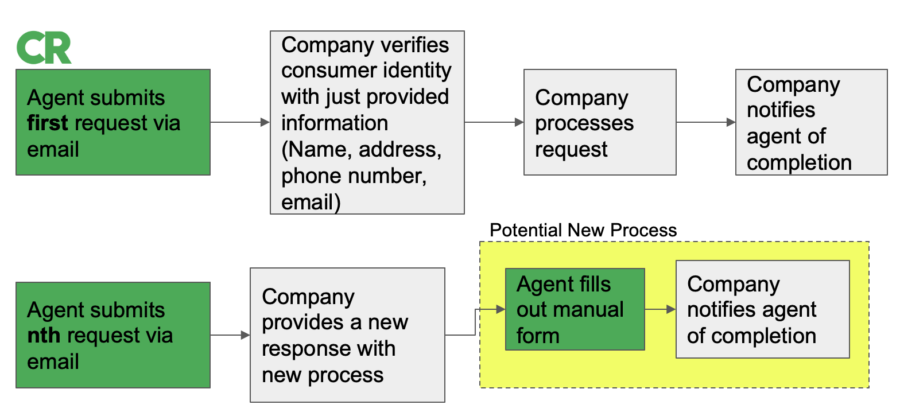
Switching flows were a small but important portion of companies in our sample: 2 of the companies we analyzed changed their request process during Permission Slip’s 90 day private beta earlier this year. Switching flows require diligence from agents to remain up-to-date on the latest processing requirements, and might break automated processes for sending requests that agents had previously set in place.
In our analysis, the companies that did switch processes switched from their own bespoke process to a form submission process facilitated by a third-party B2B privacy compliance vendor. This may suggest that an influx of requests can encourage companies to seek more sophisticated solutions for handling the requests they receive. As more states enact digital privacy regulations, we may see more companies choose to change their flows in order to keep up with increasing numbers of privacy requests. Future work might consider trends in how companies switch their processes to help authorized agents evolve their privacy operations.
(4) Authorized-Agent Action Flows
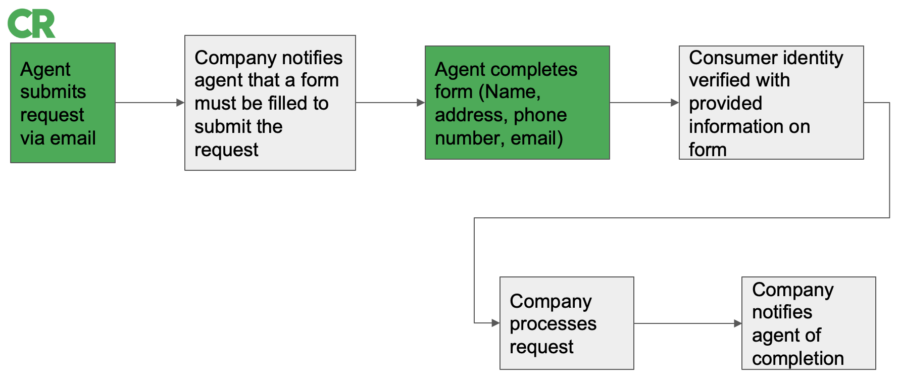
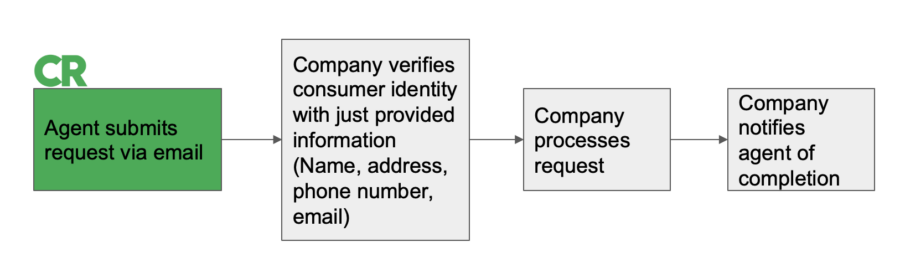
Many flows require additional action, either from the authorized agent or the consumer. Authorized-Agent Action flows require the agent to take additional action or provide additional information so that the company can process the request. Permission Slip used email as a first attempt for all requests submitted in the private beta. When agent action was needed, companies typically redirected us to re-submit the email requests via their online form.
These flows were present in 3 of the companies we studied, all of which required the agent to fill out a manual form online as part of submitting the consumer’s request. Agent action flows make up a relatively small portion of the companies in our sample, possibly related to the limitations of our sample described above. However, being able to submit requests via online form allows an agent to significantly scale up the number of companies they can send requests to. The challenge is that these forms aren’t uniform and often contain CAPTCHAs and other technologies that make automated submission hard, posing issues for agents that seek to submit requests at scale.
One way to allow both agents and companies to scale requests is through standardization. In addition to adapting submission forms to allow for agents to automate request submission, agents and companies may consider joining the Data Rights Protocol, a web protocol for sending and responding to data requests.
(5) Consumer Action Flows
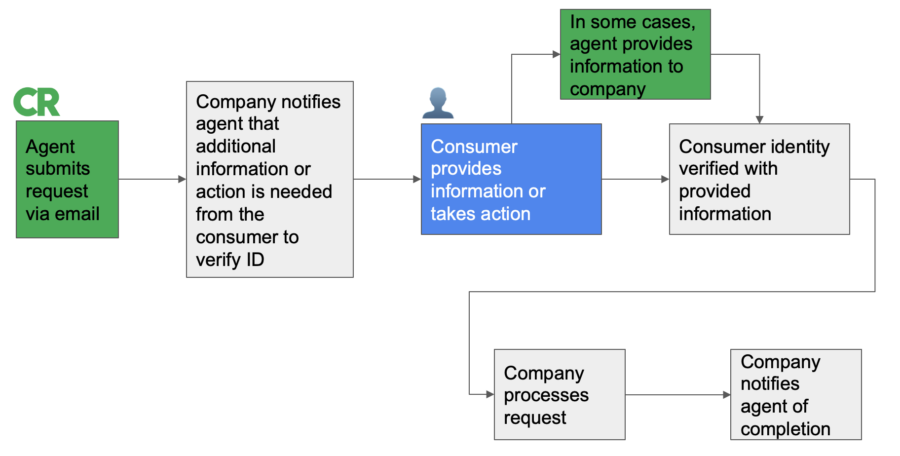
Lastly, 6 of the companies we analyzed required additional action to be taken by the consumer (consumer action flows). We identified two broad categories of additional consumer actions needed: authentication and additional identity verification.
Authentication involves a consumer logging in to a platform to confirm their identity and/or the request. This allows companies to match a request to a specific user and ensure that requests are legitimate. Log-in information is sensitive and users must log in themselves; thus agents lose visibility into these flows and can’t act as effectively on consumers’ behalf.
Additional identity verification processes typically require one additional step or piece of information to confirm the consumers’ intent to exercise their right to privacy and identify the relevant data record within the company’s database. This can involve asking the consumer for information that is highly sensitive, such as a government ID. Other requested identifiers, like a loyalty card number, are less sensitive. The main challenge for agents in handling these flows is in anticipating the back and forth required to procure this data, though one solution is for agents to proactively procure the information from consumers and provide it prior to sending the request to the company. This solution doesn’t come without risk: Agents should be wary of and prepared for the security concerns that come with operating as a central storehouse of identifiable data.
Conclusion: The state of the data rights ecosystem
The data rights ecosystem is rapidly developing: Consumers are learning how to exercise their data rights, while companies are implementing and iterating on data compliance practices. As the ecosystem develops, authorized agents will need to periodically assess how companies are handling requests in order to be able to adapt and provide value to consumers.
Authorized agents are in a unique position in the world of CCPA requests because of the number and variety of requests we send to companies. We’re hopeful that this analysis of Permission Slip’s early experiences can help companies see how their flows are commonly traversed by agents, and help agents identify opportunities to improve efficiencies. Ideally these findings will also drive agents and companies to better collaborate on handling consumer data rights requests. Analyzing company flows is an ongoing process, and we will continue to share as we learn more.
Thank you to Ginny Fahs and Maggie Oates for helpful comments on this piece.